Introduction: Why Public Keys Are the Foundation of Crypto Transactions
In the realm of blockchain and cryptocurrency, public keys are part and parcel of any and every transaction. In a centralized system, such as traditional banking, a central authority - your bank - verifies your identity prior to sending and transacting. In the decentralized structure of a blockchain in which cryptocurrencies operate, a public key serves the same purpose (identity verification) without disclosing sensitive identity data.
A public key allows for the verification of peer-to-peer transactions without any third-party intermediaries, making it a necessity for the operation of all cryptocurrencies in existence today - including Bitcoin, Ethereum, and over a thousand others.
When you create a wallet on a platform such as Binance, Coinbase, BTCDana, and others - the protocol automatically generates a pair of cryptographic keys: a public key and a private key. Your public key is effectively the address of your wallet and the identifying mark that people will use to send crypto (like an email address in the crypto space - you share your address without a care in the world knowing that it is safe for others to send you funds and if you don't share it you cannot receive funds).
Understanding public keys is the first important step to understanding cryptocurrency wallet security. Because without this understanding, the crypto landscape and how you interact with it can seem overwhelming and risky. But the moment you have an understanding of how public keys demonstrably work, you'll understand why the technology used to secure these and other transactions is considered the most secure way to transact digitally.
The Origin of Public Keys: Asymmetric Encryption and Blockchain Security
To grasp the concept of public keys, we first need to examine the technology that public keys rely upon: asymmetric encryption. Asymmetric encryption takes the approach of using mathematically related keys, referred to as public keys and private keys, respectively, which relates to how symmetric encryption implements a single shared key for both locking and unlocking data. The discovery of asymmetric encryption in the 1970s has become foundational to digital security and blockchain technology today.
In asymmetric encryption, data encrypted with a public key can only be decrypted with its paired private key, and vice versa. This feature allows a channel for communication and transfer of ownership without the need for both parties to share a secret password/code in advance. Blockchain networks, such as Bitcoin and Ethereum, are built upon this point of cryptography using Elliptic Curve Cryptography (ECC), allowing the use of smaller key sizes than RSA space while still providing very strong security.
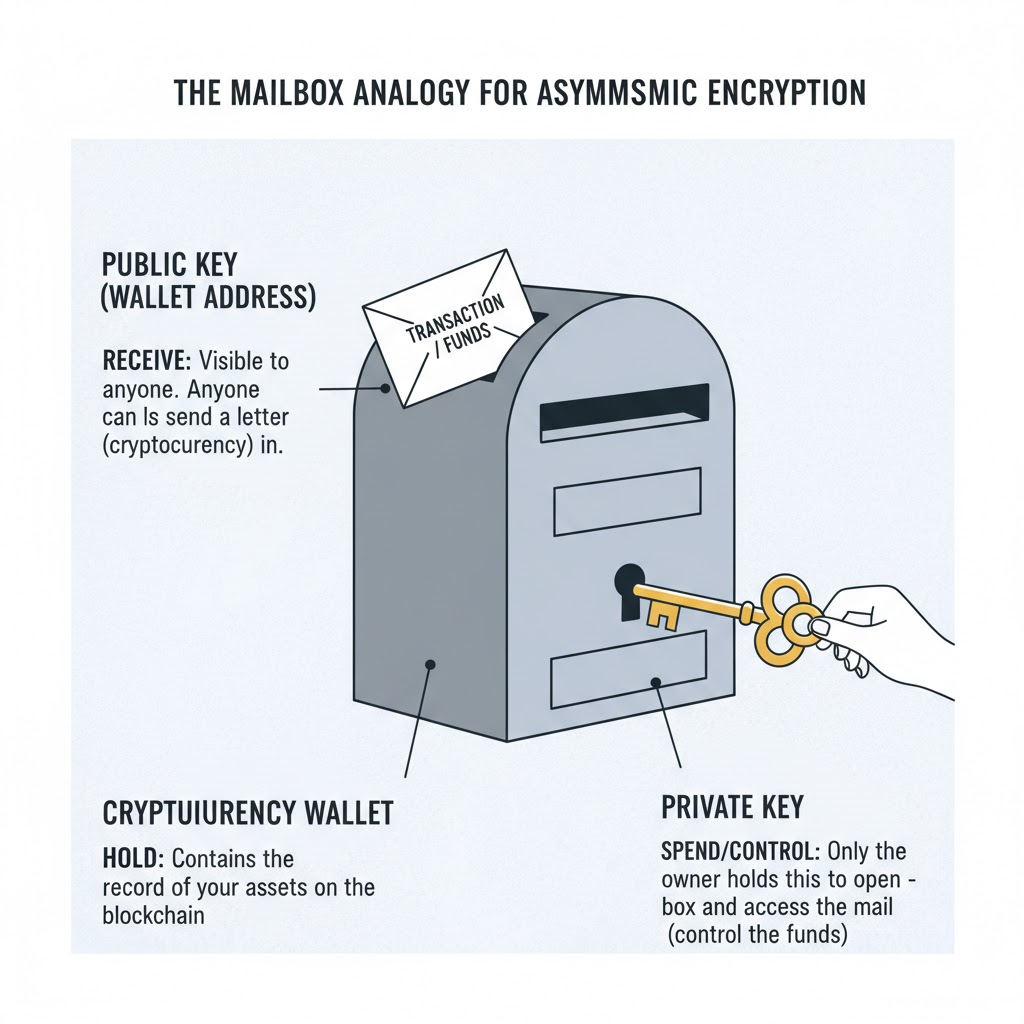
Let's use an analogy that everyone can relate to. Picture a mailbox on your front door. The opening in the box (public key) is visible to anyone, and anyone can drop a letter in your mailbox at any time. Only you have the key (private key) that opens the mailbox for you to read the letter. In our previous analogy, a letter is a transaction in crypto, and your mailbox allows anyone to send you a letter, and only the owner can read it.
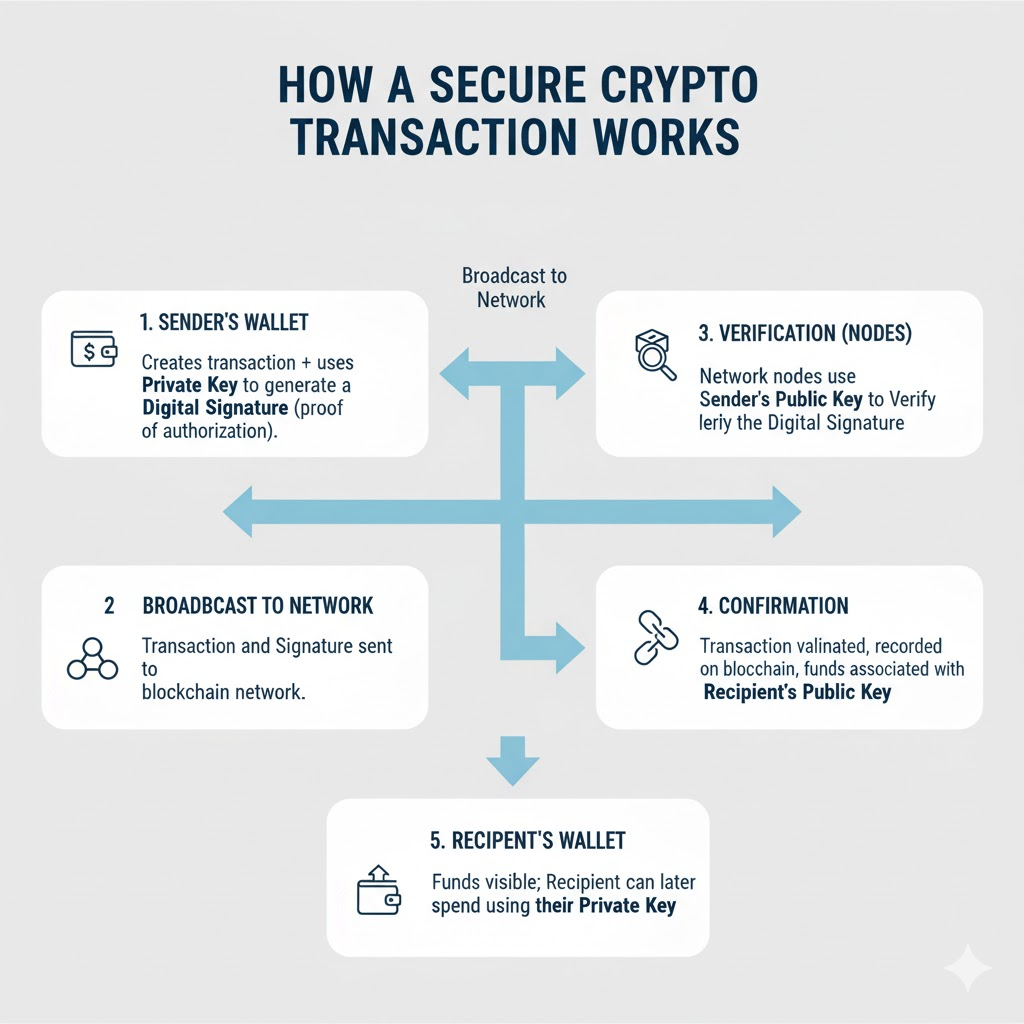
For example, in Bitcoin, when you send Bitcoin, your wallet uses your private key to create your digital signature, verifying you have authorized the transaction. Nodes on the network verify the signature using the public key. The design's benefit is that the signature signs over ownership, without revealing the private key; mathematically, the network verifies you signed the transaction, and now they do not have the secret key to control the asset.
It is important to know that public keys do not actually "hold" your cryptocurrency. Your coins are not locked inside a digital vault associated with your public key. The blockchain records who owns what and your public key is a signifier in that record. When someone looks at a Bitcoin address derived from your public key, they are not looking at a location holding your Bitcoin, they are looking at a record of transactions associated with that address.
Your public key is used to verify your identity and ownership in the blockchain, it is your proof of participation in the blockchain and guarantees the transparency and integrity of the decentralized network.
Public Key vs Private Key: Understanding Their Roles and Differences
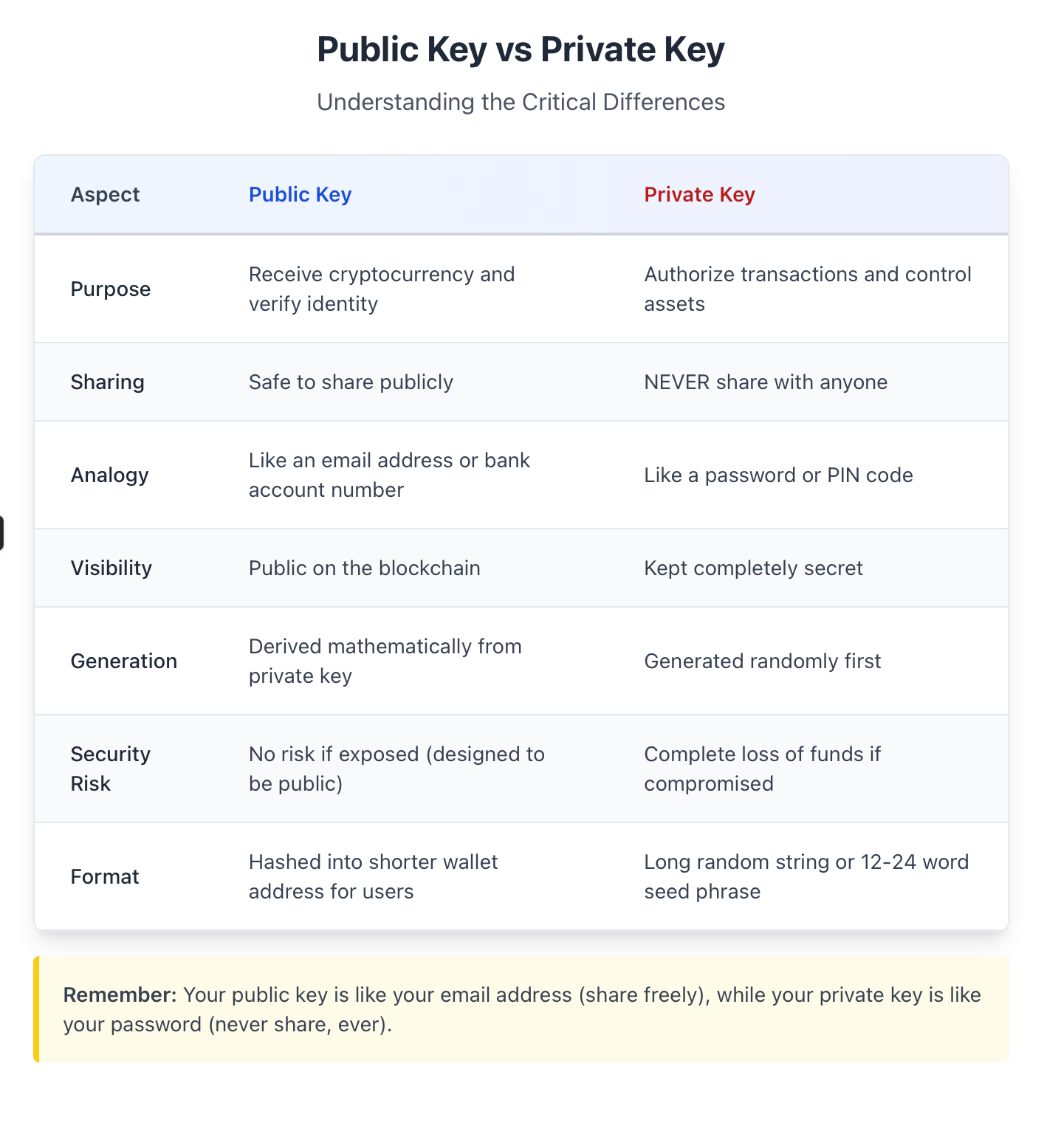
Although public keys and private keys are an inseparable pair, they serve very different purposes in terms of security in cryptocurrency. Knowing how each one functions and its associated role will allow you to secure your digital assets and use your crypto wallet securely.
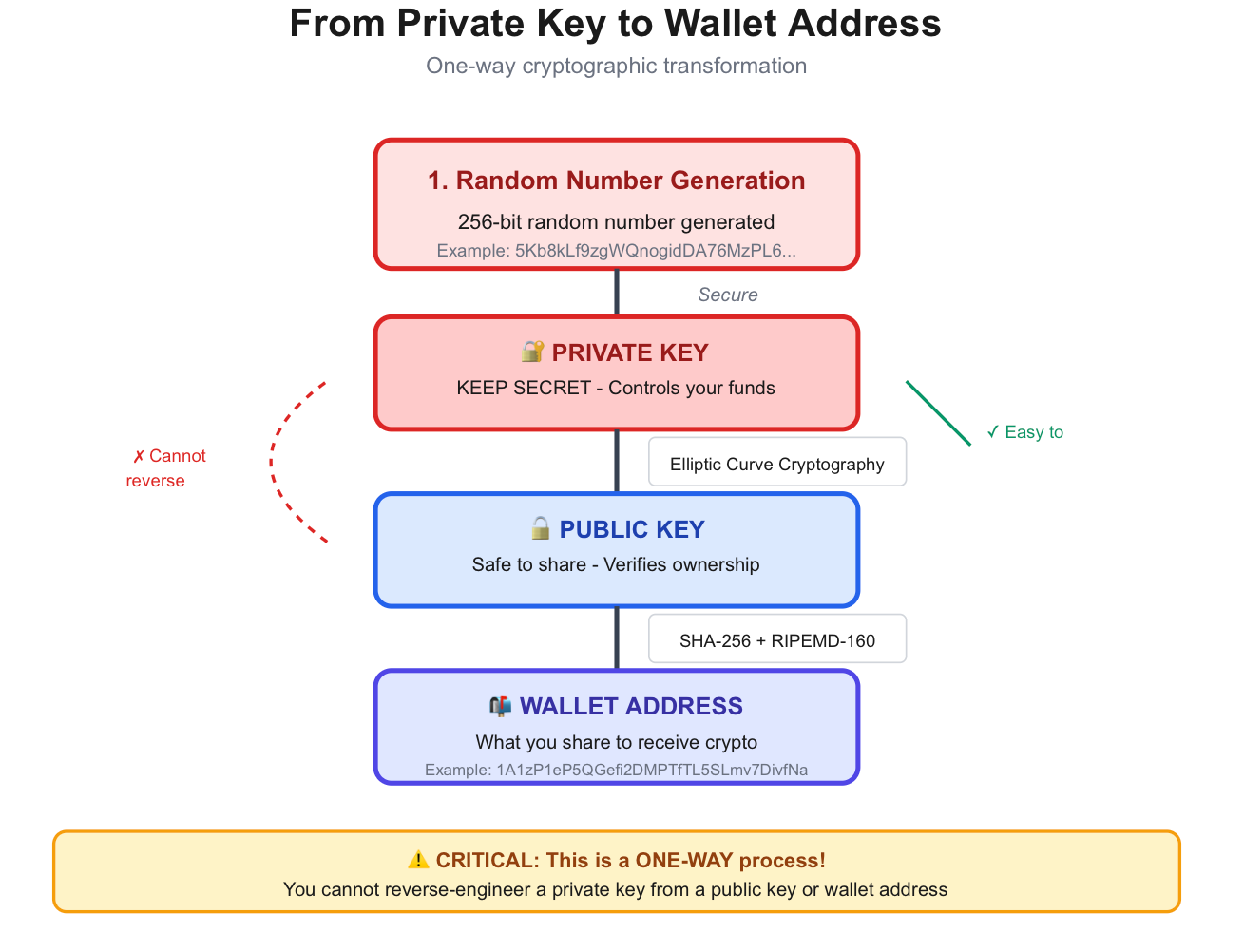
Let's break down the key differences:This relationship between these keys is elegantly simple yet very secure. When you create a wallet, your private key is created as a long string of random characters that acts as the key to all your crypto assets. The public key is created mathematically from this private key, and the wallet address is derived from the public key through hashing. This relationship is a one-way path, so no one can derive your private key from your public key and your wallet address. So, you can share your public key and wallet address with anyone because you cannot compromise the security of your assets.
Think of it similarly to how your email system works: your email address (your public key) is what you provide everyone else to contact you. Your email password (your private key) is what you protect since it grants you the ability to read messages, send emails, and control your email account. Anyone can email you just by knowing your email address, but they cannot read your messages or send emails as you without your password.
This becomes evident when you think about Bitcoin transactions. For instance, when Alice would like to send Bitcoin to Bob, Bob shares his Bitcoin address (which is generated based on his public key). Alice's wallet will generate the transaction, sign it using her private key to indicate to the network that she is authorizing the transaction, and send it to the network. The Bitcoin nodes will use Alice's public key to verify whether or not Alice's signature is legitimate. Once the transaction has been verified, that Bitcoin is now associated with Bob's public key, and Bob can prove that he owns those coins (to whoever he wants) using his private key whenever he decides to spend it.
When wallets like MetaMask or Trust Wallet are created, the app automatically creates this key pair behind the scenes for you. You will typically be given a recovery phrase (or seed phrase), usually either 12 or 24 words, which is a backup for your private key. Your recovery phrase is basically another version of your private key, and should be treated with the same level of security.
Here's the important thing to remember: you should never, ever, under any circumstances share your private key, or recovery phrase. No reputable service/support team/blockchain validator is going to ask for it. You can, however, share your public key/wallet address, which is how people will send you cryptocurrency. Both keys are crucial to the system, but only one should be kept private.
How Public Keys Work in Crypto Transactions
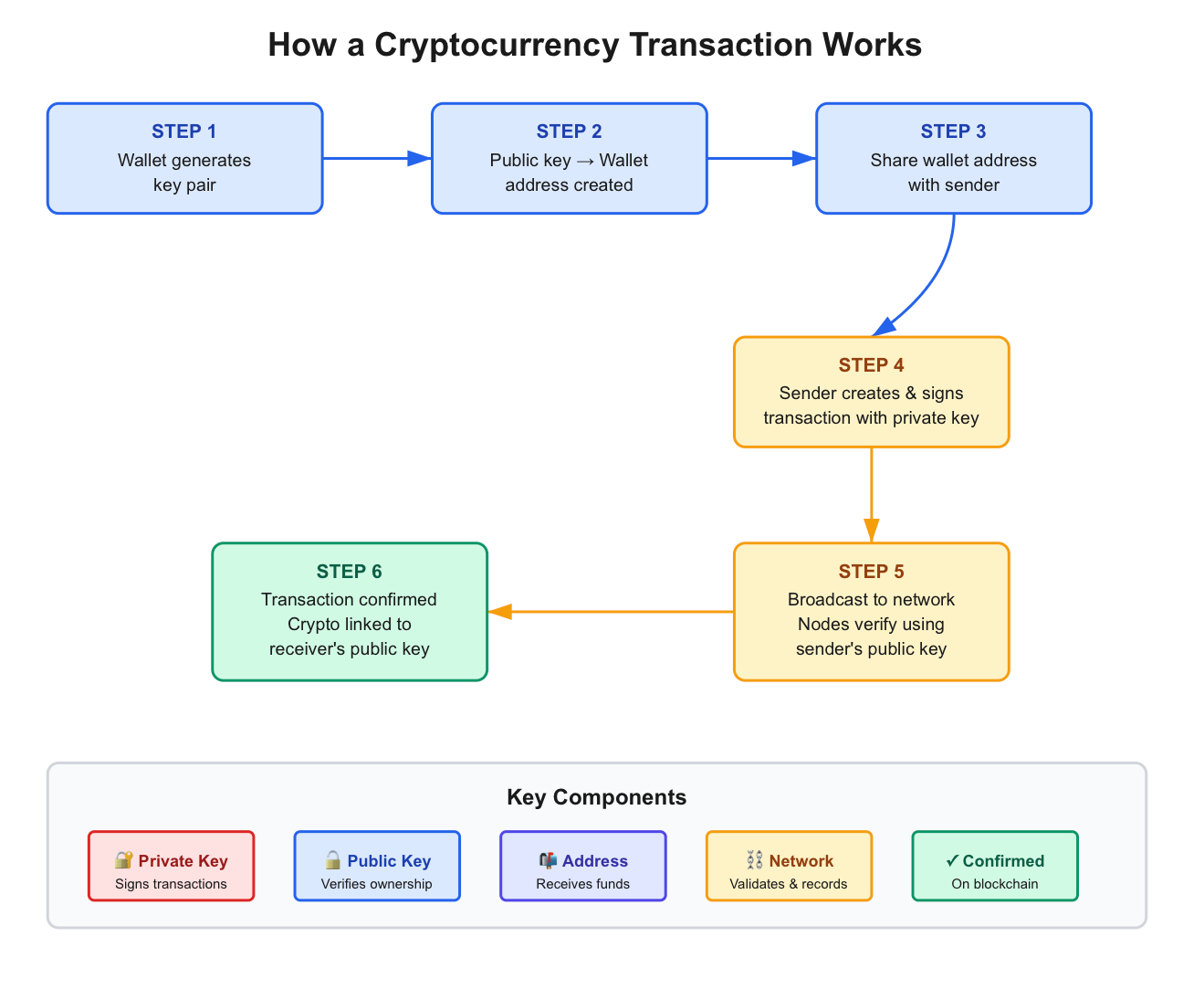
Gaining insight into the step-by-step functioning of public keys addressing cryptocurrency transactions truly demystified everything about the blockchain experience. Let's go through a typical transaction back to front and see how public keys, private keys, and the blockchain network elegantly interact with one another.
Step 1: Key Pair Generation When you create a cryptocurrency wallet ,whether through BTCDana, MetaMask, Coinbase, or any other platform ,the wallet software is programmed to generate a unique pair of keys utilising cryptographic algorithms. The software generates a random number generator to create a unique private key that would be virtually un-guessable. Then, the public key is mathematically derived from the private key using elliptic curve cryptography.
Step 2: Wallet Address Creation You are not creating a public key that you would typically share with other participants. You will endure some type of hash function on the public key (SHA-256 and then RIPEMD-160 for Bitcoin for instance) to create a shorter and more easy to relay version that would be used to represent the public key which is termed a wallet address. This is like a compressed version of your public key and what you see as those long strings starting with "1," "3," or "bc1" for Bitcoin wallets and "0x" prefix for Ethereum addresses.
Step 3: Sharing Your Address When you want to receive cryptocurrency, you share that wallet address with the sender. Think of it like giving someone your bank account number — it is safe to share, and this address cannot be used to access or spend the funds. Most wallets will generate this as a QR code that can easily be scanned to allow for even further simplicity with the transaction process.
Step 4: Creating and Signing the Transaction Once someone has sent you the crypto, their wallet creates a transaction that contains the amount and the destination (your wallet address). An important detail to keep in mind with the transaction is that the sender must sign the transaction with their private key. The signature is proof of the sender's ownership of the money and consent to the transaction. The digital signature is unique in math equation to the transaction and correspondingly to the sender's private key, which serves as good proof and evidence of authenticated ownership.
Step 5: Verifying the Transaction After the transaction has been broadcast on the blockchain network, the nodes (or computers responsible for maintaining the network) verify this transaction with the sender's public key. The nodes verify that a valid digital signature has taken place on the transaction, and that the sender indeed has a sufficient balance. Once this verification takes place the transaction is recorded permanently on the blockchain, and is linked to the next block of transactions.
Step 6: Obtaining Your Confirmation: After it has been confirmed on the blockchain (which typically takes about ten minutes for Bitcoin or seconds for other networks such as Solana), the cryptocurrency has now been associated with your public key. You will observe it reflected in your wallet balance, but it will require your private key to spend it. A simple analogy might be in the real world is to think about it as your public key is your home address; anyone can send you mail (a.k.a cryptocurrency) there, and the postal service (a.k.a blockchain network) can be assured that it will get there. However, only you (with your home key, a.k.a. your private key) can open the door and use what is inside.
It is worth mentioning that while your wallet address is related to your public key, it is not the same thing as your public key. The wallet address is a shorter, easier to use version that is easier to share, and your public key is the longer string that your wallet is using behind the scenes to verify your validity. When you transact with Bitcoin, Ethereum or USDT, the blockchain is mathematically verifying that you own the cryptocurrency using your public key, however the user sees and interacts strictly with the easier to use wallet address.
This entire process will happen without your involvement in seconds, creating the same illusion that sending a text has the same level of difficulty as a cryptocurrency transaction, with the same level of security as your bank through publicly secure forms of cryptography.
Public Key Security: What You Should Know
Although sharing public keys is safe, it is important to assess how sharing operates, and how it would affect you regarding security and privacy of your crypto assets. The blockchain's transparency is arguably one of its greatest advantages, yet it also allows for privacy concerns that each of us as a crypto user should be aware of.
The Security of Public Keys -
As it regards public keys, it is safe to share a public key and therefore share the wallet address that derives from a public key. That is literally the point of public keys! For your own exposures about public keys you can have confidence that the exposure of your public key does not necessarily allow someone to steal your funds, or transaction authorizations as would be if they had your own private key. The cryptography leveraging of algorithms are structured in a manner that even if given significant allocated compute to try to reverse engineer, it would take longer than the universe itself exists.
Of course, safe to share does not mean there is no privacy awareness of exposure when you do. Below are situational privacy risks you can consider taking to address:
Exposure of Transaction Behavior
Everything that you transacted within the blockchain is recorded, and those transactions are public. While your wallet address does not need to tie to your actual name, anyone can create a transaction history and a record of your balance from your public key. If you use the same address consistently, someone could profile your economic activity connected to your crypto: how much crypto you hold, when you transact, who you transact with, etc.
Blockchain Analytics and Tracking
Blockchain analysis companies such as Chainalysis or CipherTrace have forensic blockchain analytics that specifically track the flow of cryptocurrency on the blockchain. Law enforcement uses these services to investigate practices on the blockchain for illicit activities in a case, however, at the same time, they can also leverage this analysis to evaluate your own transaction behavior. If your wallet address can ever be potentially linked to your real identity, for example through a KYC requirement (Know Your Customer) through a crypto exchange, then all of the transactional history will remain tied to you from that wallet, forever.
Phishing and Social Engineering
While your public key is inherently secure, it can be publicly exploited (for example, your public crypto wallet address) by hackers or scammers to approach you. If a hacker observes that you have large amounts of cryptocurrency within your wallet, you could be worked on in your phishing attempts. Fake wallet sites may also be created in order to deceive you into providing your private key using social engineering.
Recommended Practices for Public Key Security
Here are just some of the basic principles you can utilize to enhance your privacy and security in crypto:
Use Hardware Wallets for Larger Amounts: Cold storage wallets, such as Ledger or Trezor, allow you to keep your private keys "virtually" offline (at least with major security). Your public key will be visible on the blockchain, but your private key never touches the online web. This makes them completely secure from an online dedicated hacking.
Create New Wallets For Each Transaction: Most wallets today (or at least offer) are structured as hierarchical deterministic (HD) wallets, which means they can easily create unlimited wallets from just one seed phrase. There is a substantial challenge to observers if you post from an unique wallet for every transaction since it will be nearly impossible for the observer to follow your trades and develop an entire set of wallets.
Exercise Caution with Public Exposure: Avoid sharing your wallet, social media, or forums publicly unless absolutely necessary. Disclosing your wallet address can be safe but does create a potential target for exploitation, especially if it is of considerable worth. If accepting donations from others, use a completely separate wallet and a separate exchange to avoid cross contamination of money tracing.
Check All Wallet URLs: Always double check URLs, and never download apps unless it comes from the official website. Fake wallet URLs and software all publicly labeled with a name, are out for your private key.
Utilize Coins with Privacy Enhancing Features: For increased anonymity, consider transacting with privacy-centered coins, such as Monero or Zcash, for transactions where total privacy is most desired.
Be Careful About Address Reuse: When you make a deposit to an exchange, the deposit address may change after a period of time or use. Always double check the address before depositing to the exchange.
At the end of the day, this boils down to maintaining a very important balance. Everyone needs to be using a public key that is meant to be public; however, using good privacy hygiene can help you manage the extent of visibility in your financial life on the blockchain. While, in the foreseeable future, the cryptographic security of a public key is next to impossible to prototype, it is still important to maintain vigilance with privacy hygiene and the role that it plays in your overall security posture in the cryptocurrency space.
Future of Public Key Cryptography in Web3 and Blockchain
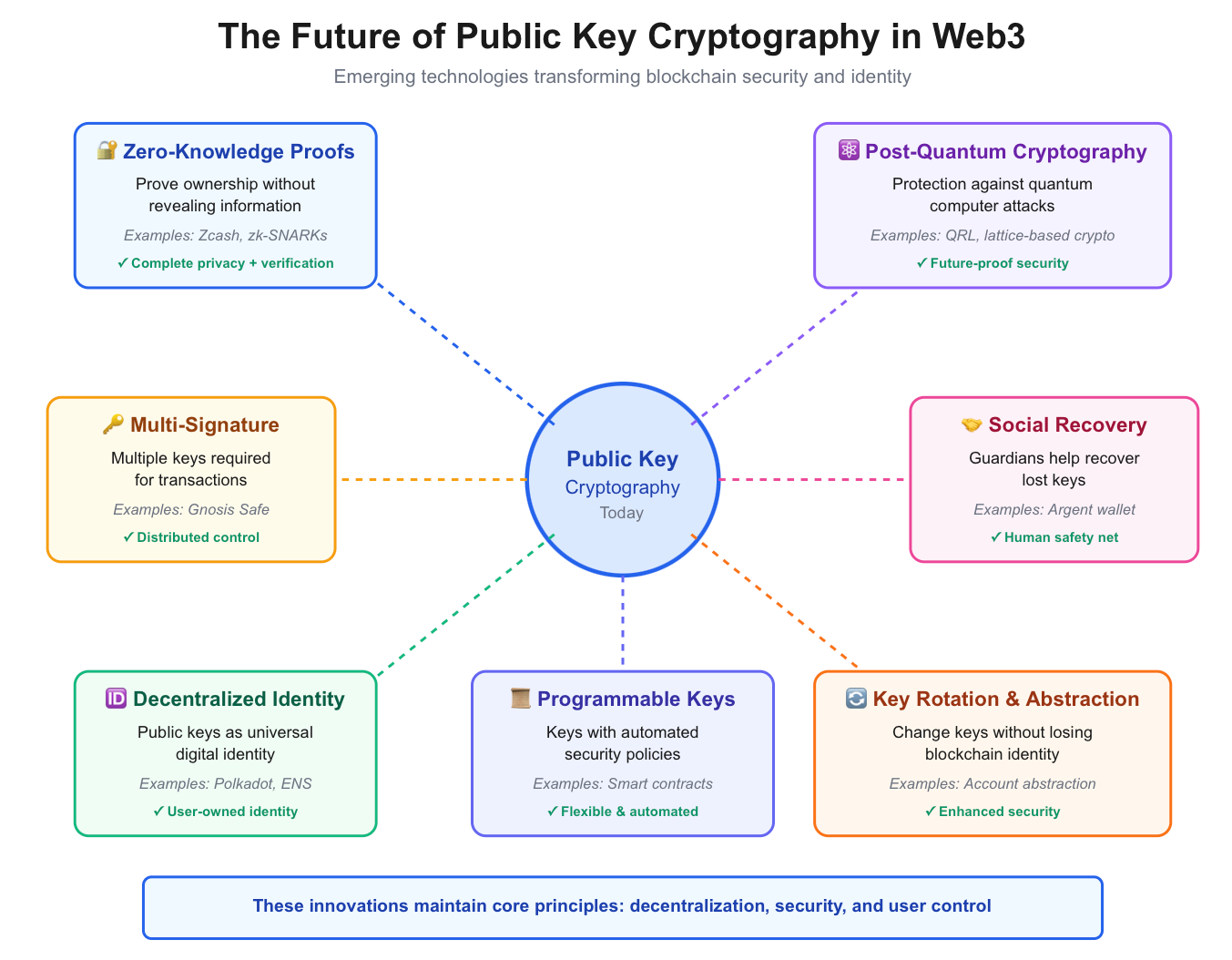
The function of public key cryptography is experiencing a rapid transformation as blockchain technology grows and Web3 comes to life as the next version of the internet. What began as a simple way to ensure that a cryptocurrency experience occurred is growing into a full suite of digital identity, ownership, and privacy for the decentralized web.
Zero-knowledge proofs (ZKPs) are one of the most innovative areas of research in cryptographic technology. It allows one party to prove to another party that they know some information (e.g., I have enough cryptocurrency to trust me with this transaction) without revealing the actual information. Blockchains like Zcash have begun to implement ZKPs to allow for entirely private transactions while maintaining the verifiability of the blockchain that makes blockchains reliable. ZKPs can be viewed as being the next step in public-key systems, evidently providing privacy without security.
Post-Quantum Cryptography: Securing the Future
Historically, public key cryptography has relied on mathematical constructs that would require an astronomical amount of time for even the fastest computers to be solved. However, quantum computers, which leverage the principles of quantum mechanics to perform calculations at speeds exponentially faster than classical computers, could potentially break the chains that public key cryptography relies on for security. The blockchain industry is already developing, studying, and implementing post-quantum cryptographic algorithms that will remain secure even in an era of powerful quantum computers in the future.
However ,it does appear that projects such as the Quantum Resistant Ledger (QRL) and their indications for their post-quantum improvements to major blockchains indicates that public key systems will remain secure for the next several decades on the blockchain, if they do transition to post-quantum methods from current methods of security.
Multi-Signature Wallets: Distributed Control
Multi-signature (multi-sig) wallets represent a major step up in key management. Rather than a single private key that controls access to one's funds, multi-sig wallets require multiple keys to authorize transactions. For example, a transfer of funds from a multi-sig wallet would generate a requirement for 2 of 3 keys to approve the transfer.
The benefits of using multi-signatures in wallets are obvious, as it creates less risk of a single point of failure, which is helpful in either a corporate environment or among Distributed Autonomous Organizations (DAOs) and financially responsible trolling individuals. There has been extensive adoption of multi-sig wallets throughout Ethereum's ecosystem among other blockchain systems, with platforms designed for smart contracts like GNOSIS SAFE leading the industry standard of usage across the web3 industry.
Social Recovery: Human-Centric Security
One major limiting factor of cryptocurrencies has been the irreversibility of the loss of private keys. Social recovery wallets work to solve this issue by allowing trusted individuals to informally serve as guardians and help you regain access to your wallet when you lose the private key. The idea of doing this has been introduced by Vitalik Buterin from the Ethereum network and is implemented in social recovery wallets like Argent. While offering this feature, social recovery wallets still maintain the security of a standard private key wallet, while also adding a human safety net. This will help make cryptocurrencies more approachable to everyday, mainstream users who may be intimidated by the sole trust of managing and holding a private key.
Decentralized Identity (DID): Public Keys as Digital Identity
Perhaps, the most impactful and radical evolution has been introducing the use of public key infrastructure as the very basis of digital identity in Web3. Decentralized identifiers (DIDs) allow users a way to actually own their identity, and control their online identity by way of a decentralized application, instead of relying on a centralized authority like Google or Facebook. Your public key becomes more than a way to receive crypto, it becomes your all-encompassing universal identifier across a decentralized web, granting access to different applications, proving credentials, and managing your digital reputation.
Projects such as Polkadot and Cosmos are establishing cross-chain identity systems that allow you to use your public key credentials across multiple blockchains. Also, there are protocols, like ENS (Ethereum Name Service), that map human-readable names to complex public keys, ultimately making Web3 no more difficult than Web2.
Integration with Smart Contracts: Programmable Keys
The combination of public keys and smart contracts enables programmable security policies. For example, imagine keys that automatically expire, keys that only work with the biometric confirming you are engaged in a large transaction, or time-locks for increased security. This is not science fiction, it is being built today on platforms like Ethereum, and will allow enormous flexibility when it comes to how we manage our digital assets.
Key Rotation and Account Abstraction
Future systems will implement key rotation, which is the ability to change your keys without changing your blockchain identity or moving your assets. When combined with account abstraction (which separates your blockchain identity from the keys that control it), wallets will be more secure and flexible. If a key is compromised, for example, you can quickly rotate to new keys without losing your transaction history or on-chain reputation.
The public key is transitioning from a basic cryptographic function into the keystone of digital sovereignty in Web3. As the technology matures, managing cryptocurrency will be both safer and more manageable, allowing blockchain capability to become increasingly likely for mass adoption, all while retaining the core principles of decentralisation and user control that make this revolutionary.
Frequently Asked Questions About Public Keys (FAQ)
Is my public key the same as my wallet address?
No, but the two are closely related. Your wallet address is derived from your public key and involves secondary cryptographic hashing. The longer version, which is user sharing, is called your wallet address. Think of your public key as the source code and your wallet address as the compiled, shortened version that the user would interact with. Your public key is used for cryptographic verification behind the scenes, with your wallet address being what the user sees in the wallet app.
Can someone steal my crypto if they know my public key?
No, definitely not. Your public key is meant to be shared freely and securely, that's the point. The algorithms that create key pairs have been developed in such a way that knowing your public key doesn't enable an attacker or the person who has your public key to figure out your private key (this would take billions of years using every bit of computational power available today). Your funds are safe, although your transaction history is still public, which does raise privacy issues.
Can a public key be hacked or reverse-engineered?
In practical terms, no. The mathematical relationship between a public key, and a private key is a one-way function. It is easy to generate a public key from a private key, but reversing this is mathematically impossible with today's technology. The security is based on math problems, like elliptic curve discrete logarithms, that not even the fastest supercomputers available would be able to solve in a reasonable amount of time. This is the basis for why the security of the currency is placed in the private key; there is no need to care about public keys.
Why do I get multiple addresses from my wallet?
Today’s wallets all utilize a hierarchical deterministic (HD) wallet structure which can generate an unlimited number of addresses from a single seed phrase. This increases your privacy because you can use a brand new address each time you transact with anyone. This makes it much harder for anyone who may be watching to tie all these transactions together and then calculate your total holdings. The great part is that all these addresses are controlled and associated with your one private key (seed phrase). You will then always have access to your funds across all of the addresses. Most wallets take care of this for you too.
What will happen if I accidentally share my public key?
Nothing bad will happen -- you are actually supposed to share it! This is how people send you cryptocurrency! The confusion often originates in people thinking they shared their private key when they only shared their public key or wallet address. As long as you have never shared your private key or seed phrase, your funds are safe and completely secure.
Does each type of cryptocurrency use its own public key system?
Yes, different blockchains are likely to use different cryptographic algorithms to generate keys. Bitcoin generally relies on ECDSA (Elliptic Curve Digital Signature Algorithm) with the secp256k1 curve, whereas some newer systems might use EdDSA or other variations. But the main idea behind the public and private keys are the same with all cryptocurrencies, a public key to receive and verify, and a private key to authorize any transactions.
May I have the same public key on multiple different blockchains?
For the most part, no. Each blockchain network generates a unique key pair, and their addresses are made using different formats. For example, a Bitcoin address looks entirely different from an Ethereum address. That said, some wallets have the ability to derive multiple blockchain addresses from the same seed phrase. This can simplify managing multiple cryptocurrencies with a single recovery phrase.
Conclusion: Master Your Wallet Security
When it comes to understanding public keys, it's far too easy to get lost in the lingo. But this is actually a crucial point of learning for the cryptocurrency landscape and to protect your digital assets. As we've discussed, public keys provide the backbone for security on blockchains and allow us to transact trustlessly, confirm ownership and create a decentralized financial system that is fundamentally changing our views on money and digital identity.
The simple beauty of public key (and private key) cryptography is that it is simple and elegant: one key you share freely to receive funds and authenticate your identity and one key you protect with your life to control your assets. This has become a remarkably robust system, with billions of dollars worth of cryptocurrency transacted every day and security that makes the traditional financial system jealous.
But getting to know the system is not enough, you need to employ and practice these principles to protect your investments. Keep the principal lessons in mind: share your public key and wallet address freely when you need to get funds, but protect your private key and recovery phrase with your life. If you have significant holdings, use a hardware wallet. If you want higher privacy, consider creating new wallet addresses. And remember to always verify an application's authenticity before trusting it with your keys.
As blockchain technology transitions to Web3 through improvements like zero-knowledge proofs, post-quantum cryptography, and decentralized identifications, the fundamentals become increasingly valuable. The public key is no longer a means of making a cryptocurrency transaction; it is becoming the basis for digital sovereignty, creating agency over your financial assets, your online identity, and your digital presence.
Whether you are just beginning to learn about crypto or want to improve your knowledge of blockchain security, understanding the principles underlying public and private keys puts you in position to participate in decentralized technology while reducing the risk to send money and for the mismanagement of data. The next step is to put this into practice: securing your existing wallets, reading about how different cryptocurrencies implement these principles, and continuing your education as the technology matures.
Ready to put your knowledge into action? Start your secure cryptocurrency journey with BTCDana, where cutting-edge security meets user-friendly trading. Join thousands of traders who trust BTCDana to protect and grow their digital assets with confidence.
Start Trading Safely on BTCDana → | Learn more about protecting your crypto investments and explore our comprehensive guides to mastering digital asset security.